Lottery Security and Compliance for Retail Operators
Comprehensive lottery security and compliance solutions with automated audit logs and enterprise-grade protection for secure operations.
Lottery security and compliance is essential for lottery resellers who need to protect sensitive transaction information and meet regulatory requirements. Our lottery audit software provides comprehensive lottery reconciliation software features including automated audit logs for lottery operations. This enables instant lottery audit capabilities with tamper-proof audit trail recording that ensures lottery security and compliance from every transaction.
Start Free 15-Day Trial Request Security Assessment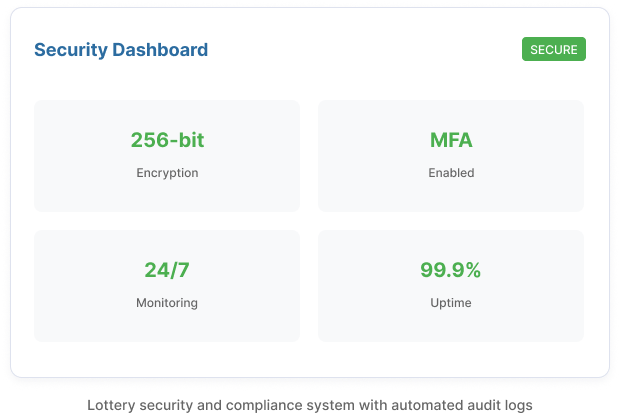
Lottery Security and Compliance Features
Advanced Data Encryption
Enterprise-grade lottery data security with end-to-end encryption for all data in transit and at rest using industry-standard AES-256 encryption. This ensures comprehensive lottery ticket security and supports lottery commission compliance requirements.
- AES-256 encryption at rest
- TLS 1.3 encryption in transit
- Hardware security module (HSM) key management
- Database-level encryption
Secure Access Controls
Role-based access control with granular permissions and multi-factor authentication for all users. Our lottery security and compliance system includes lottery reconciliation software features that provide secure lottery management system controls for lottery retailer compliance.
- Multi-factor authentication (MFA)
- Role-based access control (RBAC)
- Session management and timeout
- Concurrent session controls
Automated Audit Logs for Lottery Operations
Comprehensive lottery audit software with automated audit logs for lottery that track all user actions, data changes, and system access for compliance. This enables instant lottery audit capabilities and supports lottery compliance checklist requirements.
- Complete activity logging
- Tamper-proof audit logs
- Configurable retention policies
- Compliance reporting
